About the Data in This Report
Orchid Security leverages the latest technology advancements in the fields of observability, prompt engineering and large language models to analyze all identity- managed or unmanaged - as coded and utilized within each enterprise application.
The applications analyzed for this report have been deployed throughout some of the largest organizations in North America and Europe, spanning industries such as financial services, health care, retail, manufacturing, energy and more. The findings presented are based on the anonymized and aggregate telemetry collected between April 1, 2025 and March 31, 2026.
Our objective is to shed light on the true state of identity security. The most common and persistent control gaps, account exposures, at risk behaviors and more. We hope it guides organizations about where to pay extra attention within their own identity security posture. Despite the valuable tools, strong corporate policies and existing documentation, our findings uncover many flaws that lay beneath the surface of managed identity. Hopefully, this report will provide valuable insight and direction to both executives and practitioners.
Executive Summary
The Invisible Elements of Identity Now Overshadow The Visible Ones
If 2026 is remembered for one identity-related inflection point, it will be this - the year of Identity Dark Matter, the unseen, unmanaged layer of enterprise identity that every IAM program has always known existed but never fully measured - crossed a threshold. The invisible elements of identity now outnumber the visible ones.
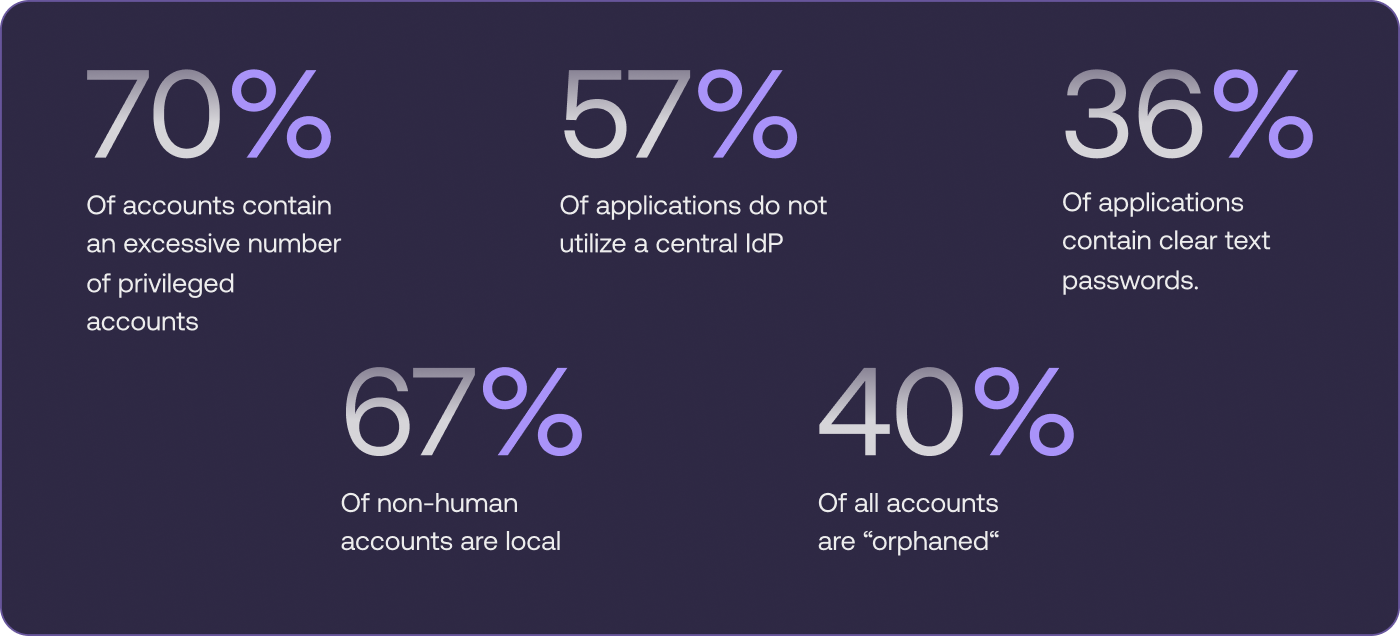
With 57% of applications failing to route authentication through a central, secure identity provider, the majority of enterprise application access occurs outside the IAM stack. Further, two-thirds of non-human identities are authenticated and authorized locally, inside applications, with no directory, no IdP, and no central oversight. 40% of all accounts belong to users who no longer exist in HR systems, referred to as “orphan accounts.” And one out of three applications stores credentials in plaintext.
None of this is new. These gaps have always existed. What is new is what arrives next.
Industry analysts project that 40% of enterprise applications will embed task-specific AI agents by end of 2026 - up from less than 5% just one year prior. AI agents do not create new identity risk. They operationalize existing risk. They are efficiency-driven actors that inherit whatever credentials are available, follow whatever authentication path works fastest, and operate at machine speed across the identity surface your IAM stack cannot see.
That surface is the one documented in this report.
A last note, these findings do not exist in isolation. They compound. An orphaned account, authenticated locally, with excessive privilege and credentials stored in plaintext, is not five separate risks - it is one open door that any agent, human-directed or autonomous, can walk through without triggering a single alert.
Despite the pace of agentic adoption, research consistently finds that fewer than one in five enterprises has a mature governance model in place for the AI agents they are deploying. The gap between deployment speed and identity readiness is where breaches happen.
Key Findings
1. Excessive Privilege
Least privilege is not a new concept. It appears in virtually every security framework, every compliance requirement, and every corporate security policy we have encountered. And yet, in 70% of the applications we analyzed - more than two in three - the number of accounts with elevated privilege was excessive.
What we found:
- Admin-level access is granted broadly, often as the default configuration rather than an exception
- Root-level access is assigned to third-party vendors, frequently without review or expiration
- Weak default credentials on privileged accounts across multiple industries and application types
Why it matters
Excessive privilege has always expanded the blast radius. A compromised account with admin access can do significantly more damage than a compromised account without it. That risk is not new.
What is new is the actor. An AI agent does not request access - it inherits whatever exists. It does not evaluate whether a privilege level is appropriate; it uses what is available to achieve its objective. When 70% of applications run on over-permissioned accounts, an agent’s first move is also its most dangerous: it takes the fastest path, which is also the broadest.
Recent cloud disruptions attributed to well-intentioned but ungoverned agent actions demonstrate this failure mode at production scale. The accounts were not compromised. The agents simply used what was there.
2. Invisible Non-Human Accounts
The standard IAM model for non-human identities has always carried a known weakness: these accounts are typically granted broad, standing access on the assumption that their behavior is predetermined and repetitive. A service account that runs the same job on the same schedule poses a manageable, bounded risk.
That assumption no longer holds, with the adoption of Agent AI.
Two-thirds of all non-human accounts in our analysis are established, authenticated, and authorized locally, within the application itself. No directory. No IdP. No central IAM control. They are invisible to the tools your security team uses to monitor identity activity.
Across geographies, we observed meaningful variation: non-human accounts in the US were more likely to be centrally managed than those in EMEA, where local implementation dominates. In the EU, both human and non-human accounts were more likely to carry restricted privilege - a pattern that may reflect regulatory pressure rather than deliberate architecture.
What we found:
- Two-thirds of all non-human accounts have no connection to a central directory, IdP, or IAM control
- Local authentication is the dominant implementation pattern for non-human identity across industries
- Geographic variation exists, but the majority of environments carry significant invisible NHI exposure regardless of region
Why it matters:
Analysts estimate that machine identities already outnumber human identities by a factor of 40 to 80 in enterprise environments. Apply the 67% invisible rate to that multiplier, and the scale of the unmanaged layer becomes difficult to overstate.
Traditional non-human accounts were predictable actors. They did the same thing, on a schedule, without deviation. AI agents are a categorically different kind of non-human identity. They are objective-driven, not task-driven. They adapt. They take the path that best achieves their goal - not the path that was expected.
Deploying an objective-driven actor into an environment where 67% of non-human identity is invisible to every oversight mechanism is not a configuration decision. It is a risk decision. And right now, most enterprises are making it without realizing it.
3. No secure identity provider (IdP)
Routing authentication through an identity provider is one of the most foundational controls in modern identity security. It enables SSO, enforces MFA, provides a single inspection point for anomaly detection, and gives the security team visibility into who is accessing what, when.
In 57% of the applications we analyzed, this control does not exist.
Authentication is handled locally. Access paths bypass global policies. The justifications we encounter most often are familiar: contractors needed access, the legacy directory was already in place, the application did not support SSO integration. Each is understandable individually. Collectively, they describe an environment where the majority of authentication decisions are happening in a space no central control can observe.
What we found:
- Direct or local login paths that operate entirely outside global identity policies
- Bypass typically justified by operational necessity - contractor access, legacy systems, vendor requirements
- Common in applications with standalone directories or legacy authentication frameworks
Why it matters:
Threat actors have long understood that local authentication paths are less monitored and less defended than centralized ones. They look for the door that does not log who walked through it.
AI agents authenticate the same way service accounts do: through whatever path is available and functional. A 57% bypass rate means the majority of your applications contain an authentication path that does not log, does not enforce policy, and cannot be monitored in real time. For an agent operating at machine speed across dozens of applications simultaneously, that is not an edge case. It is the default environment.
4. Orphan accounts
Active accounts for users who can no longer be found in the human resources (HR) system and are presumed to have left the company or changed their credentials, accounted for 40% of all identities across analyzed applications.
What we found
- Legacy accounts from past acquisitions that were never deprovisioned
- Accounts tied to personal email addresses outside of HR lifecycle management
- Active, credentialed accounts with no current owner in up to 60% of identities in some environments
Why this matters
Threat actors find it far easier to log in than hack in. Active accounts that are clearly forgotten- dormant or orphaned- present a wealth of entry points. We discovered more than 1,000 confirmed, currently active accounts across our customers whose credentials are exposed on the dark web. Further, 22% of such accounts help elevated privileges. Proper identity lifecycle management is a critical aspect of IAM hygiene. Learn more from research analyst Katya Donchenko.
5. Credentials stored insecurely
In one out of three applications analyzed, credentials are not just stored locally - they are stored in plaintext. Embedded in codebases, configuration files, and automation scripts, these credentials are accessible to any actor who has gained entry to the environment, without any additional decryption or exploitation required.
The pattern is most common in machine and service account configurations. It is also distressingly common in software delivered by third-party vendors, who embedded credentials directly into the applications they built and deployed - often with the excessive privilege described in Finding 1.
What we found:
- Credentials embedded in codebases, configuration files, and automation scripts across a third of analyzed applications
- Especially prevalent in machine and service account configurations
- Vendor-embedded cleartext credentials present in multiple applications, frequently carrying excessive privilege
Why it matters:
Cleartext credentials require no exploitation to use. They require only access, which an attacker who has reached the application layer already has, and which an AI agent operating within the environment has by default.
Agents do not brute-force credentials. They read configuration files. In 1 in 3 applications, those files contain everything an agent needs to act with full authority: credentials, in plaintext, often with admin-level access, provided by a vendor whose own systems may still hold a copy.
This is the definition of a pre-positioned attack surface. The credential is already exposed. The only question is which actor finds it first.
6. Toxic Combination
Each finding in this report represents a meaningful risk on its own. In combination, they represent something worse: compounding exposure where the total risk exceeds the sum of its parts, and where remediation priority becomes a matter of identifying which combinations create the most exploitable conditions.
The following combinations appeared most frequently and carry the highest risk in our analysis. The final column reflects a reality that was not a factor in previous years’ assessments: the agentic amplifier.
The IAM team has too much to do and too little time to do it. Identifying and remediating the specific combinations that create the greatest exploitable conditions is not optional prioritization - it is the only practical path to meaningful risk reduction at scale. These combinations are where to start.
Where This Leaves Us
Every gap in this report was always exploitable. What’s changed is the exploiter.
Identity Dark Matter has always existed beneath the visible surface of enterprise IAM, eroding its foundation. It was acknowledged in policy exceptions, legacy application carve-outs, and the quiet understanding that the central IAM stack never really covered everything. It was manageable when the actors operating in that invisible layer were slow, manual, or bounded.
AI agents are none of those things.
They are fast. They are objective-driven. They utilize whatever identity infrastructure exists in the environment they operate within. And as of 2026, they are deployed in the majority of enterprises - often without the governance structures, the identity visibility, or the runtime oversight required to understand what they are doing.
The five findings in this report are not abstract vulnerabilities. They are the specific, pre-existing conditions that continue to expose enterprises to compromise by threat actors and now put an enterprise’s agentic deployment at risk of becoming a business inhibitor rather than productivity enhancer.
Orphaned accounts give agents unmonitored expansion points. Invisible NHIs give agents ungoverned operating credentials. Local authentication paths give agents invisible routes. Cleartext credentials give agents immediate alternative access. Excessive privilege gives agents maximum blast radius.
None of this requires an attacker. It requires only an agent doing its job in an environment that was not ready for it.
The practical path forward is sequential: address the Identity Dark Matter first, then deploy the agents with proper authorization. Organizations that invert this order are not adopting AI responsibly - they are leaving the keys to their environment strewn about where autonomous agents can find them, even as the security team cannot see them.
Orchid Security provides two resources to support this work: a checklist to clean up the most common Identity Dark Matter within your own environment, and a framework for expanding your IAM program for the agentic AI era. Both are available at orchid.security.
The team has provided two resources- one a buyer’s guide for uncovering identity dark matter within your own organization and the other key requirem
How Orchid Security Can Help
Orchid Security shines light on Identity Dark Matter and enables organizations to eliminate it - establishing a strong identity security posture and a defensible foundation for agentic AI adoption.
- See what IAM cannot
Orchid analyzes identity as it is actually implemented inside your applications - every account, every authentication path, every credential - not just what is visible to your IAM stack. The 67% of non-human identities authenticated locally, the 57% of applications bypassing your IdP, the 40% of accounts your HR system no longer recognizes: Orchid finds all of it.
- Govern what happens at runtime
Knowing where the gaps are is necessary but not sufficient. Orchid enables organizations to enforce identity controls at the application layer, in real time, without rewriting applications or replacing existing IAM investments. Access does not determine security. What happens after access does.
- Build a foundation for agentic adoption
The organizations that deploy AI agents safely are the ones that understood their identity surface before the agents arrived. Orchid provides the identity observability, the control plane, and the runtime governance required to make agentic adoption a security conversation, not a security incident.
Understanding, let alone maintaining, identity security posture across any large organization- with its diverse and always evolving application estate- is a constant challenge.
Remember, that estate includes applications created by different developers, at different times- when technology, regulations and cyber risk were different- and even by different organizations if acquisitions were part of the growth strategy.
Any approach, but especially an automated one, that provides a comprehensive and accurate view into the true state of identity, is hugely valuable to CISOs. Especially when it can surface all of the identity flows coded in each application. We know that many threat actors are adept at finding the alternate or forgotten ways into our organizations, and this report highlights the most common exposures we need to look out for (and address).
The insights shared here are instructive for every cyber security professional.
- 48%
Storage of hard coded, cleartext credentials or use weak hashing
- 44%
Authentication paths that bypass the corporate Identity Provider
- 40%
A lack of baseline controls like rate limiting, account lockout and password complexity
- 37%
Outdated or non-standard authentication protocols
- 37%
of applications failed to enforce access controls fully or at all
Checklist to Identify the Top Missing Identity Controls
Download Checklist
Discovery and Gap Analysis: Continuous Visibility Beyond the Known
Orchid delivers continuous, telemetry-driven visibility into identity implementations across all automatically discovered applications regardless of geography, technology stack, or existing compliance knowledge. This capability empowers organizations to uncover both commonly missed controls and hidden identity mechanisms that conventional audits and reviews often fail to detect.
No Prior Context or Manual Input Required
Unlike traditional assessment and onboarding processes that rely on interviews, documentation, or involvement from app owners or developers, Orchid's analysis is entirely autonomous. It requires no prior data points, tribal knowledge, or manual onboarding, making it ideal for large, fast-changing environments.
Save Time, Save Money — Harness Your True Identity Landscape
By eliminating the need for human-led discovery, context-gathering, or code walkthroughs, Orchid significantly reduces the time and cost of identity posture management. It accelerates both discovery, gap analysis and remediation cycles including onboarding, freeing up security teams and engineering resources to focus on higher-impact work while utilizing the organizational siloed identity tools.
Checklist, Fully Covered
Our platform aligns directly with the Checklist to Identify the Top Missing Identity Controls and many more providing instant, actionable insights on where your applications stand and what needs attention.
- January 2025
PowerSchool Breach
Cybercriminals reportedly used stolen credentials to access a support portal that lacked MFA, exposing sensitive student and parent data.
- March 2025
Jaguar Land Rover Incident
A threat actor used stolen credentials to infiltrate the company’s Jira system, allegedly stealing over 700 internal documents.
- April 2025
Verizon Data Breach Investigations Report
Verizon Identifies Stolen Credentials as Top Breach Entry Point In their latest report









