Introduction
Today, identity is the foundation of most every organization, as well as its cyber security program. As the CISO at Repsol- a learning multi-energy company in Europe- Javier Quintera Garcia notes, “everything is based on identity” and looking at cyber threats he continues, “the new attack field is the identity.” His head of cyber security, David Corral adds, “Another challenge we face is that there is a clear increase in the regulatory scrutiny that we are having, and identity and access management is one of the areas these regulations put more focus.” Accordingly, it is essential to have a sound identity and access management program with controls in place; for cyber security, for regulatory compliance and for the business.
Identity and the Cyber Threat Landscape
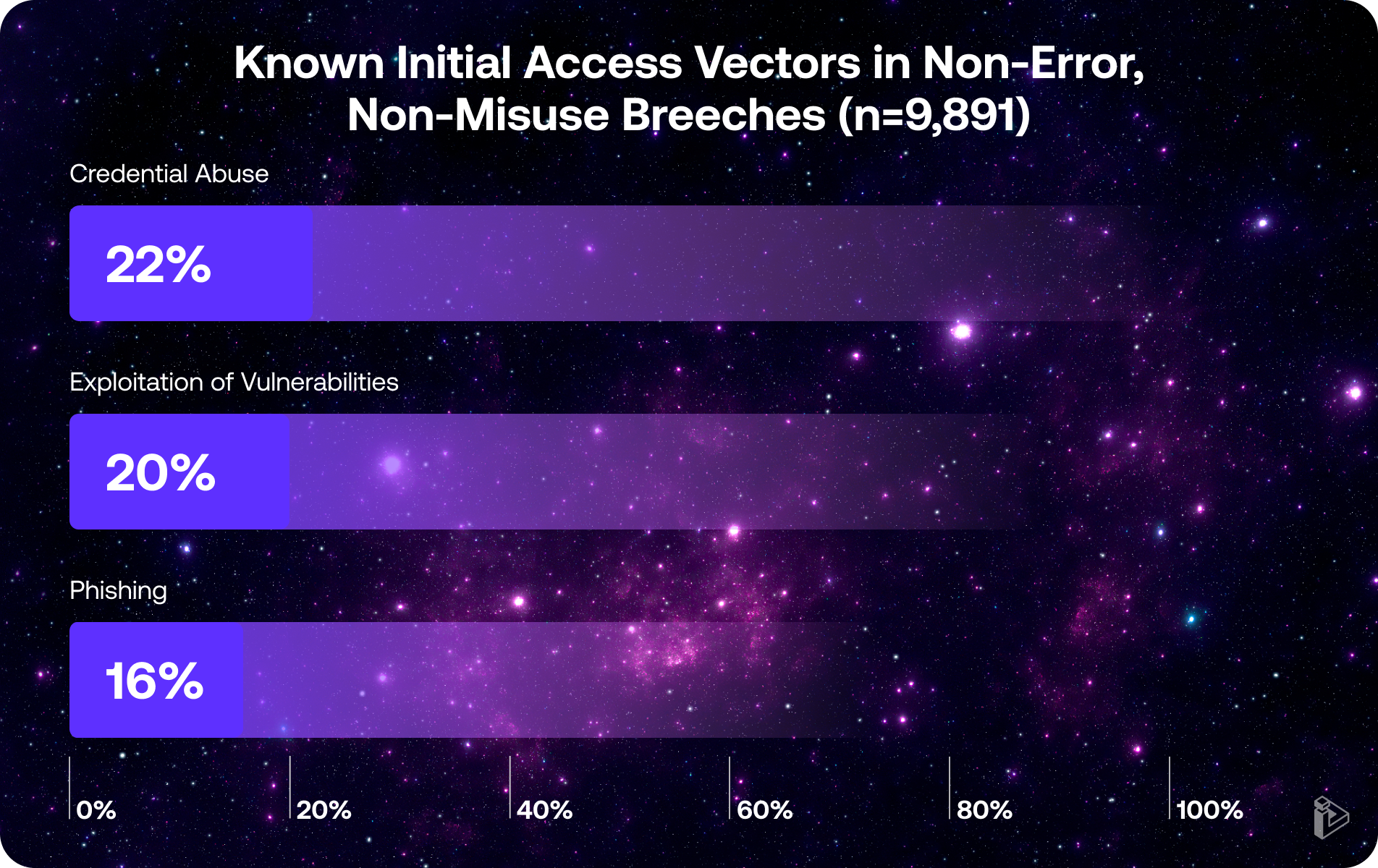
According to the 2025 Verizon Data Breach Investigation Report, credential abuse is the #1 method leading to breaches, And as the German Federal Office for Information Security (BSI) reports, broken access control is the second most common exploitation by cybercriminals in 2025.
The impact of this type of risk can be seen in the breach of a major automotive manufacturer, who had production lines shut down for 5 weeks after threat actors gained entry via stolen credentials to a ticketing system. The BBC reports that this cyber security incident is the costliest in UK history. But that manufacturer was by no means the only European organization that experienced a breach due to an identity exposure. Very large European enterprises in retail, telecommunications, energy management and more were also breached similarly.
Regulatory Environment
In addition to cyber risk, proper identity and access management is also a cornerstone of many European regulations. For example, the NIS 2 (Network and Information Security) Directive requires proper access controls to systems, including multi-factor authentication specifically. Similarly, the Digital Operational Resilience Act (DORA) requires that organizations establish strong measures to ascertain the unique identification of individuals and systems that will access the financial entity’s information. Further, the EU General Data Protection Regulation (GDPR) at its foundation requires that organizations take appropriate measures to prevent unauthorized access or accidental loss of data. Failure to do so constitutes a data breach, requires reporting and may lead to fines and other penalties. Interestingly, the recent EU AI Act classify AI use cases by risk, including the data it can access, so having transparent access controls and reporting (by account, including AI / Service Accounts) is required.

Business Health
Beyond the potential business and financial impacts of potential cyber security incidents or regulatory fines or penalties for non-compliance, running a traditional identity and access management program is expensive. Routine activities, such as onboarding a new business implication into the existing identity tool stack (10,000 Euros per application) or demonstrating regulatory compliance (100,000 Euros per audit) result in a seven figure spend each year. Plus the periodic introduction of a major IAM tool or change of vendor can easily double that spend for multiple years. In fact, for most organizations, identity and access management is one of the largest line items in the cybersecurity budget.
The State of Identity in Europe
IAM Maturity
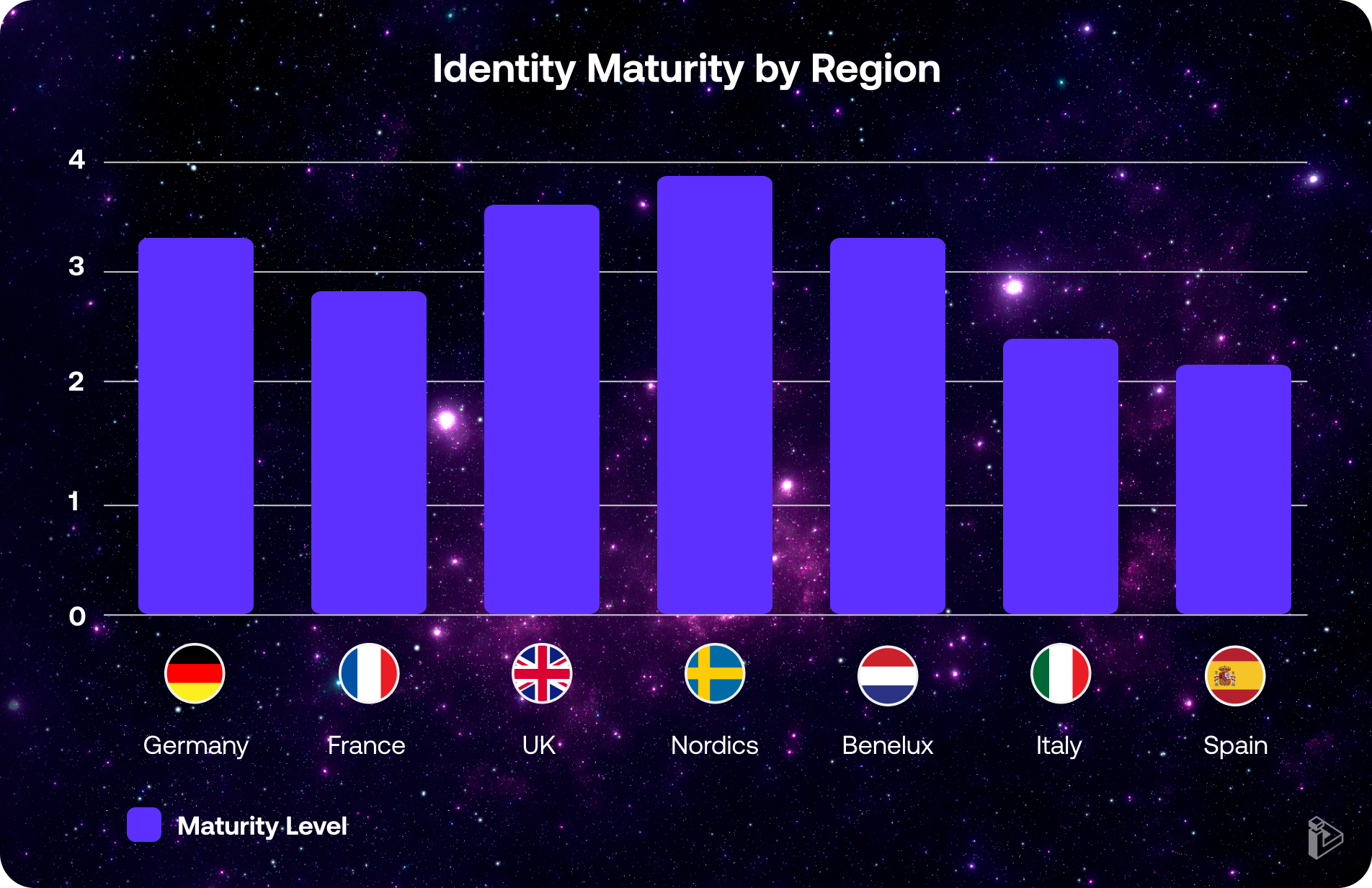
Given the level of cyber risk, regulation and recurring spend, one might expect the level of IAM maturity and Europe to be quite high- characterized by prevalent use of a central identity provider, controlled by a privileged access management (PAM) tool and well-managed by an identity-governance and administration (IGA) solution, as well as appropriate processes in support.
However, as a region, maturity is actually average (3 out of 5) at best; with common use of IdP, but limited PAM and IGA utilization. Of course, the Nordics exceed the norm, while Spain and Italy lag. But most EU organizations cluster between Level 2 (Basic IAM- some IdP utilization) and Level 3 (Integrated- as described previously), indicating significant opportunity for advancement toward managed and intelligent identity control plane.
Rampant Identity Exposure
As a result, looking at the real-world state of identity, we find that the unmanaged and often invisible layer of identity (“identity dark matter”) has now reached 51% of all identity implemented throughout European enterprises. This includes:
- Applications that are unmanaged by choice or ignorance
- Authentication that is handled locally rather than by a central identity provider
- Access that is overpermissioned and ungoverned over time
- Accounts that have gone dormant or are orphaned entirely
- Weak or missing controls- for log-in rate control, password complexity, MFA, etc.
And it leaves organizations more exposed than they know, despite the deployment of IAM tools and passing compliance audits.
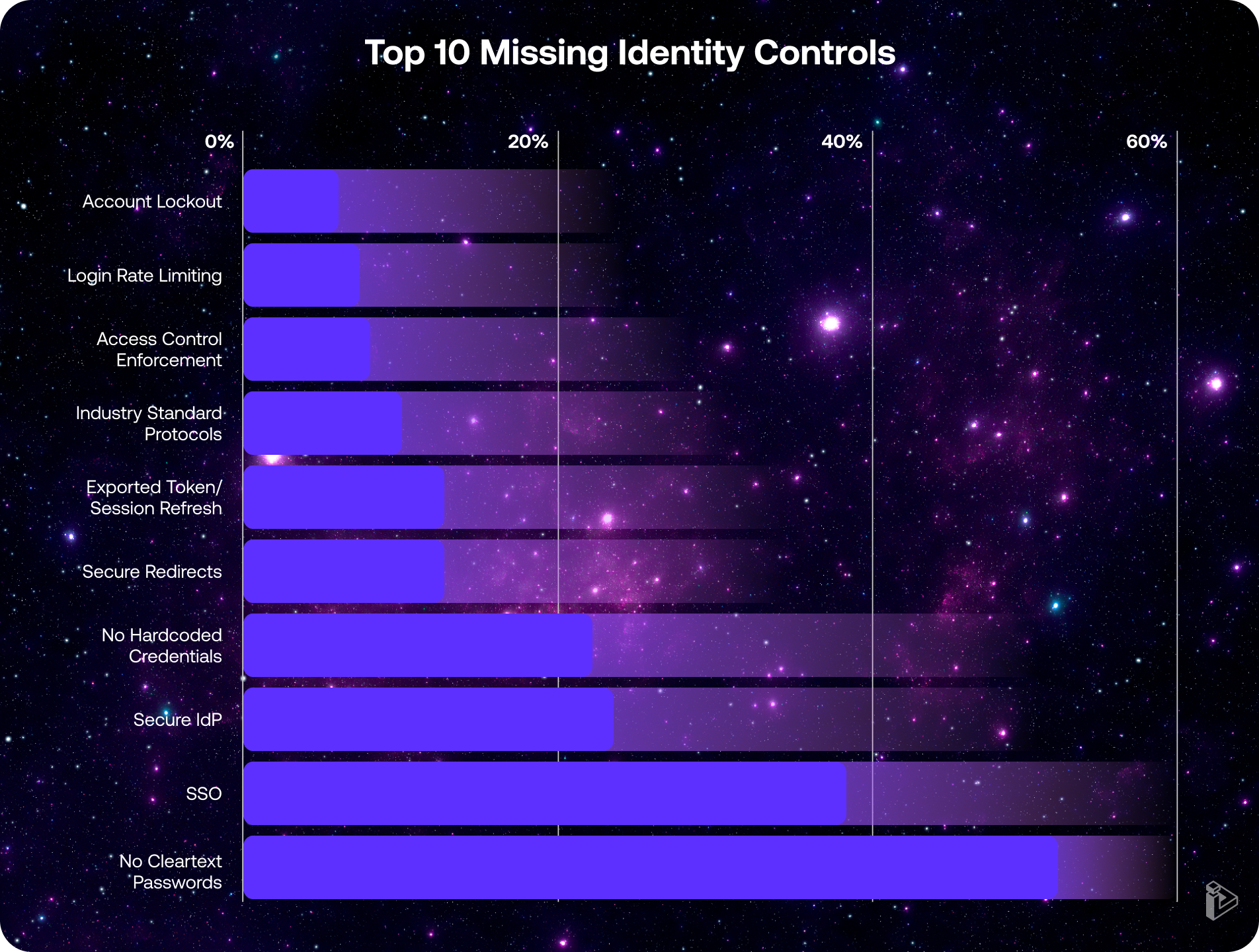
To date, in Orchid Security Identity Security Gap: 2025 Snapshot, analysis of identity as implemented within enterprise applications throughout Europe and across industries uncovered an alarming prevalence of hardcoded passwords stored in cleartext, as well as a surprising percent of authentication flows utilizing neither single sign-on (SSO) nor a central identity provider (IdP) at all. Further, a significant number of applications failed to require tokens with a defined date of validity/expiration, let alone the refresh of tokens on a regular basis. Finally, although identity hygiene was quite good compared to North America, there were still instances of applications that did not rate limit, or even monitor, login attempts as well as those that failed to lockout accounts based on unsuccessful login attempts.
The Fundamental Reason for Exposure
You may wonder how this state of exposure is possible and the answer lies at the heart of identity and access management design. By nature, identity is implemented within each application- either natively or through integration with IAM tools- at the discretion of the developer. As a result, regardless of IAM tooling deployed, corporate policies on paper or even application design documentation, the only true measure of identity happens at the application source. And the average enterprise has hundreds, typically thousands and sometimes tens of thousands of applications.
As a result, it is very common that:
- A local office or line of business develops or purchases a new application without going through the central deployment process, including onboarding into the IAM stack, or that a legacy application is deemed too difficult to onboard.
- “Break-glass” emergency access accounts exist, service accounts for a single application are added or 3rd party access is implemented directly in the application.
- Broad, rather than granular, roles and permissions get defined for certain applications. Users receive access to more applications than they actually use and / or accounts may be forgotten before users leave the role or company.
- Basic hygiene is overlooked, or accepted, for expediency or as “good enough.”
Software Analyst Cyber Research has proposed a taxonomy to define the different areas of identity dark matter.

What Organizations Can Do to Understand (and Manage) Their Risk
Whether the concern is cyber, regulatory or financial risk, there are 10 questions to ask yourself about your identity and access management program.
- Can I see all applications in my environment, including those we host ourselves, not just the ones registered in IAM / CMDB or kept modern by others as SaaS?
- Do I know every authentication flow and protocol in use, not just the primary one that may be compliant with corporate policy, regulations and best practices?
- Can I map all authorization policies inside each application, not just the most common ones covering the majority of users?
- Can I identify orphaned, inactive, over-privileged and service or otherwise unused accounts, not just those managed in the primary directory?
- Do I have visibility into local credentials and alternate shadow identity paths?
- Can I demonstrate which apps/flows/ accounts are covered by which controls, especially when required by compliance frameworks (PCI, HIPAA, GDPR, NYDFS, SOX)? And do I know the strength of each control?
- Can I continuously monitor for drift- changes made to go live, through patches or as part of major upgrades- in permissions or policies?
- Can I prioritize remediation based on risk and compliance impact? More importantly, can I assign, track and confirm their completion?
- Can I prove compliance with policy, process and resolution with evidence directly from applications and user activity?
- Can I scale this across thousands of apps in hybrid and multi-cloud environments?
An honest, accurate and complete assessment will give you a good sense of the state of identity throughout your organization, including areas of greatest exposure. The more you answer “no” or “not sure” to these questions, the greater your identity risk.For help answering these questions, visit orchid.security.
Understanding, let alone maintaining, identity security posture across any large organization- with its diverse and always evolving application estate- is a constant challenge.
Remember, that estate includes applications created by different developers, at different times- when technology, regulations and cyber risk were different- and even by different organizations if acquisitions were part of the growth strategy.
Any approach, but especially an automated one, that provides a comprehensive and accurate view into the true state of identity, is hugely valuable to CISOs. Especially when it can surface all of the identity flows coded in each application. We know that many threat actors are adept at finding the alternate or forgotten ways into our organizations, and this report highlights the most common exposures we need to look out for (and address).
The insights shared here are instructive for every cyber security professional.
- 48%
Storage of hard coded, cleartext credentials or use weak hashing
- 44%
Authentication paths that bypass the corporate Identity Provider
- 40%
A lack of baseline controls like rate limiting, account lockout and password complexity
- 37%
Outdated or non-standard authentication protocols
- 37%
of applications failed to enforce access controls fully or at all
Checklist to Identify the Top Missing Identity Controls
Download Checklist
Discovery and Gap Analysis: Continuous Visibility Beyond the Known
Orchid delivers continuous, telemetry-driven visibility into identity implementations across all automatically discovered applications regardless of geography, technology stack, or existing compliance knowledge. This capability empowers organizations to uncover both commonly missed controls and hidden identity mechanisms that conventional audits and reviews often fail to detect.
No Prior Context or Manual Input Required
Unlike traditional assessment and onboarding processes that rely on interviews, documentation, or involvement from app owners or developers, Orchid's analysis is entirely autonomous. It requires no prior data points, tribal knowledge, or manual onboarding, making it ideal for large, fast-changing environments.
Save Time, Save Money — Harness Your True Identity Landscape
By eliminating the need for human-led discovery, context-gathering, or code walkthroughs, Orchid significantly reduces the time and cost of identity posture management. It accelerates both discovery, gap analysis and remediation cycles including onboarding, freeing up security teams and engineering resources to focus on higher-impact work while utilizing the organizational siloed identity tools.
Checklist, Fully Covered
Our platform aligns directly with the Checklist to Identify the Top Missing Identity Controls and many more providing instant, actionable insights on where your applications stand and what needs attention.
- January 2025
PowerSchool Breach
Cybercriminals reportedly used stolen credentials to access a support portal that lacked MFA, exposing sensitive student and parent data.
- March 2025
Jaguar Land Rover Incident
A threat actor used stolen credentials to infiltrate the company’s Jira system, allegedly stealing over 700 internal documents.
- April 2025
Verizon Data Breach Investigations Report
Verizon Identifies Stolen Credentials as Top Breach Entry Point In their latest report









