Executive takeaway
LLMs and especially agentic LLM systems are optimized for efficiency, they minimize steps, reduce uncertainty, and seek the shortest path to an objective (see supporting resources below). In cyber terms, that “efficiency bias” maps perfectly onto identity hygiene gaps, orphaned accounts, dormant local users, stale service identities, and over-permissioned tokens, because these are the lowest-friction routes to real access. This is why “the perimeter is identity” and it’s moving fast: AI is shifting from advisor to operator, and operators will take shortcuts by design.
.png)
Why LLMs are “Lazy” (but really efficient) by Design
LLM-based agents are trained and engineered to:
- Optimize for goal completion: take actions that most directly satisfy the prompt/objective.
- Reduce cost and latency: fewer steps, fewer tool calls, less back-and-forth.
- Exploit available affordances: use whatever access already exists rather than requesting new approvals.
- Operate “on the loop”: run long task chains with minimal human intervention, especially when connected to tools.
Agents also optimize for telemetry friction. They’ll prefer access paths that don’t require approvals and don’t light up centralized monitoring, so “quiet” identities (local users, long-lived tokens, legacy auth) need to be treated as first-class signals, not edge cases.
That is “laziness” in the best product sense, less friction, more throughput. But it becomes dangerous when the environment contains identity shortcuts.
The Abuse Pattern: Shortcut-Seeking + Identity Hygiene Issues
In a modern enterprise, identity isn’t only in your centralized and well-managed IAM. It’s also embedded in:
- Local accounts inside applications
- Service identities, agent-AI identities, and tokens
- Legacy directories and external domains
- Unmanaged permissions and ad-hoc authentication paths
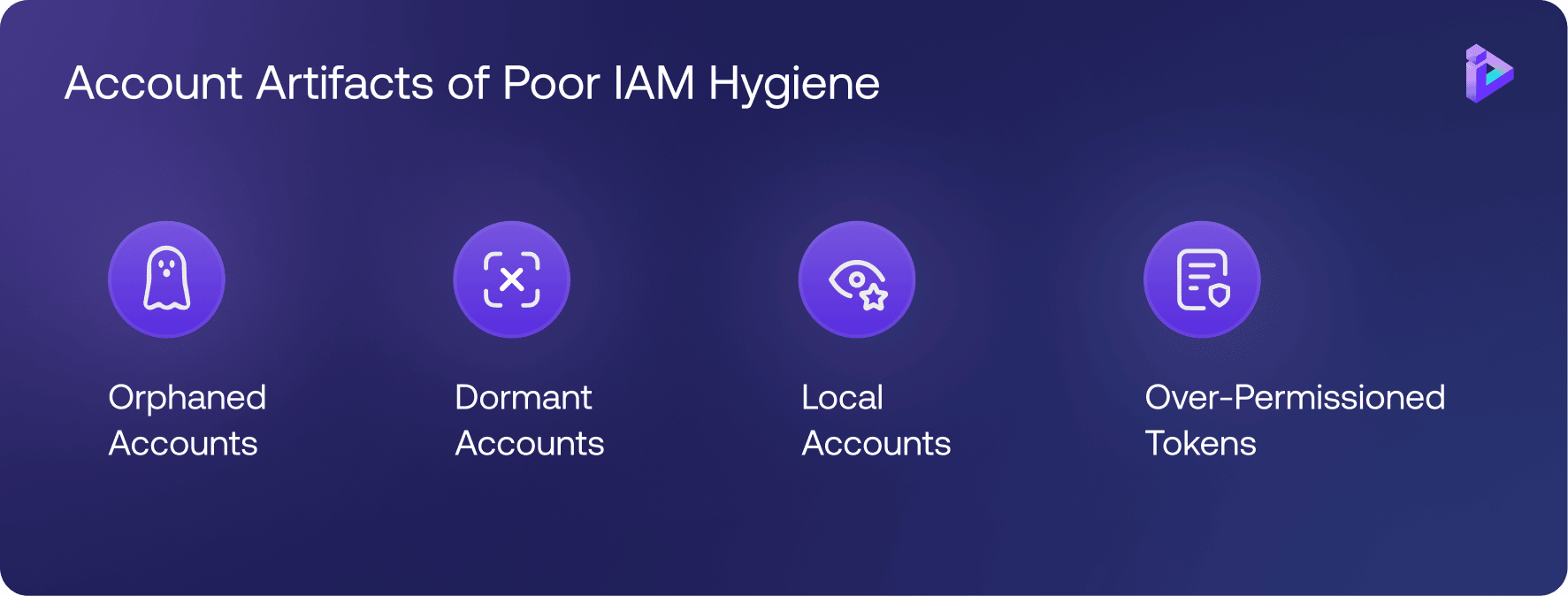
Those are exactly the artifacts that accumulate hygiene problems:
- Orphaned accounts - no real owner, never removed; if you can’t map account → team/manager, it’s effectively orphaned
- Dormant accounts - rarely used; typically 90+ days with no activity; and rarely monitored; data: dormancy is multi-signal- auth + API usage + data access, not just last_login
- Local accounts - bypass SSO/MFA and centralized controls; data: bypass paths often never hit SSO logs, so “clean IAM” can be a false negative
- Over-permissioned tokens / service identities - high power, low governance; data: risk = granted scope vs used scope; you need action-level logging to see the gap)
A shortcut-seeking agent doesn’t need “creative hacking” first. It starts with: “What already works?”
This becomes a graph search at machine speed, identities × apps × auth paths × permissions × data. If those edges aren’t observable and correlate-able, defenders reconstruct stories; agents simply traverse the graph. If there’s an orphaned local admin, a dormant service identity, or an over-scoped token that allows the agent to respond to the prompt, of course the agent will gravitate there because it’s the fastest route to success.
Why this Gets Worse with Agentic Attacks (Anthropic Case Study)
Anthropic’s report describes a campaign where attackers used an AI system not just for advice, but for autonomous execution across the intrusion lifecycle, recon, vulnerability research, exploit development, credential harvesting, and data staging/exfiltration at speeds and volumes that are “physically impossible” for humans.
The key change isn’t just speed, it’s volume and breadth: thousands of small identity events across many apps. If your identity telemetry isn’t normalized and joinable, you’ll drown in low-signal noise at the moment you need fast scoping.
Key implications for identity hygiene:
- Scale turns “one neglected account” into a systemic failure. An agent can enumerate and test identity paths across many apps quickly.
- Humans only step in at decision points. That means the agent will be rewarded for finding the easiest path before a human notices the pattern.
- Even with hallucinations, agents still win on economics. The report notes hallucinations occurred, but the overall throughput advantage remains substantial.
Net: as “AI operators” become more common, identity hygiene becomes the cheapest, most reliable attack surface.
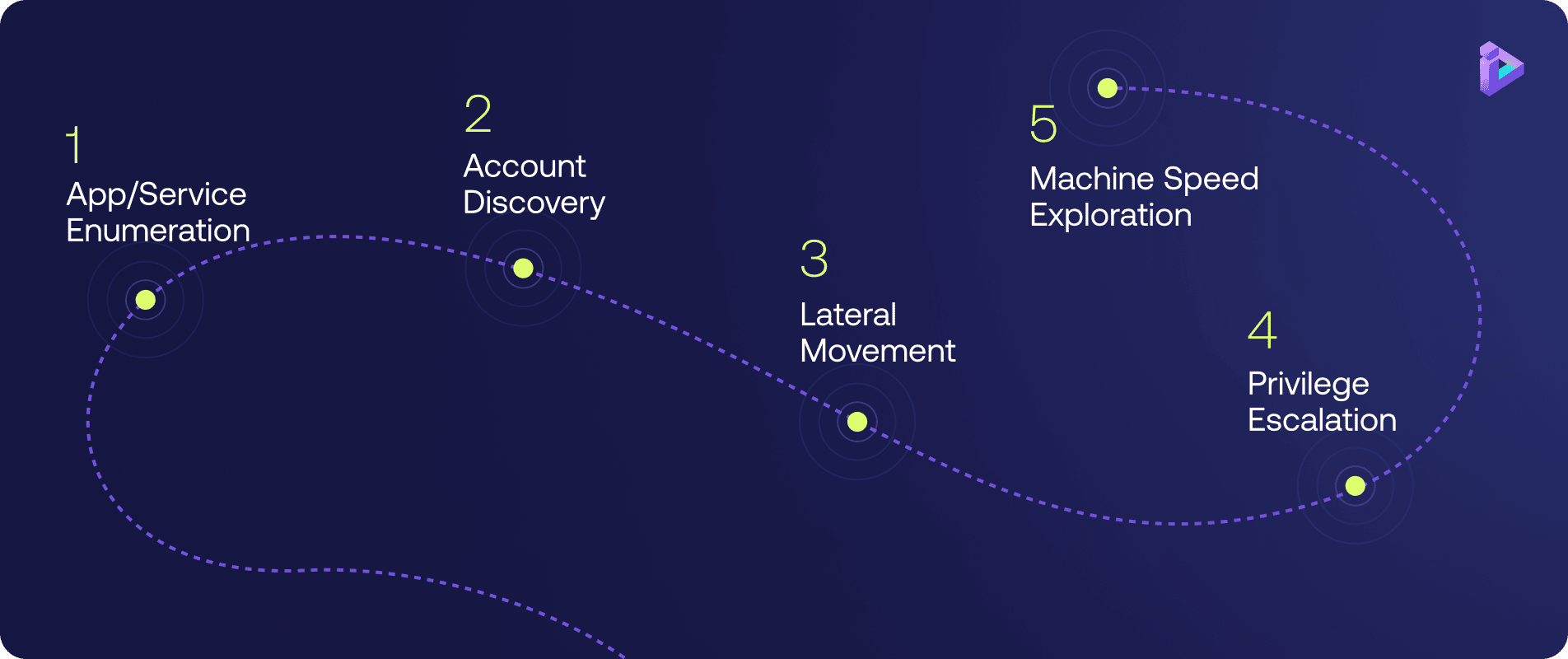
What this Looks Like in The Real World
- Agent enumerates apps/services → finds unmanaged auth paths
- Discovers dormant/local/orphaned identities → attempts authentication
- Uses “good-enough” access to pivot laterally
- Finds higher privilege via stale entitlements / tokens
- Moves fast, documents everything, repeats at machine speed
This is not “AI is evil.” Its AI is efficient.
Practical Controls that Blunt Shortcut Abuse
Understanding, let alone maintaining, identity security posture across any large organization- with its diverse and always evolving application estate- is a constant challenge.
Remember, that estate includes applications created by different developers, at different times- when technology, regulations and cyber risk were different- and even by different organizations if acquisitions were part of the growth strategy.
Any approach, but especially an automated one, that provides a comprehensive and accurate view into the true state of identity, is hugely valuable to CISOs. Especially when it can surface all of the identity flows coded in each application. We know that many threat actors are adept at finding the alternate or forgotten ways into our organizations, and this report highlights the most common exposures we need to look out for (and address).
The insights shared here are instructive for every cyber security professional.
- 48%
Storage of hard coded, cleartext credentials or use weak hashing
- 44%
Authentication paths that bypass the corporate Identity Provider
- 40%
A lack of baseline controls like rate limiting, account lockout and password complexity
- 37%
Outdated or non-standard authentication protocols
- 37%
of applications failed to enforce access controls fully or at all
Checklist to Identify the Top Missing Identity Controls
Download Checklist
Discovery and Gap Analysis: Continuous Visibility Beyond the Known
Orchid delivers continuous, telemetry-driven visibility into identity implementations across all automatically discovered applications regardless of geography, technology stack, or existing compliance knowledge. This capability empowers organizations to uncover both commonly missed controls and hidden identity mechanisms that conventional audits and reviews often fail to detect.
No Prior Context or Manual Input Required
Unlike traditional assessment and onboarding processes that rely on interviews, documentation, or involvement from app owners or developers, Orchid's analysis is entirely autonomous. It requires no prior data points, tribal knowledge, or manual onboarding, making it ideal for large, fast-changing environments.
Save Time, Save Money — Harness Your True Identity Landscape
By eliminating the need for human-led discovery, context-gathering, or code walkthroughs, Orchid significantly reduces the time and cost of identity posture management. It accelerates both discovery, gap analysis and remediation cycles including onboarding, freeing up security teams and engineering resources to focus on higher-impact work while utilizing the organizational siloed identity tools.
Checklist, Fully Covered
Our platform aligns directly with the Checklist to Identify the Top Missing Identity Controls and many more providing instant, actionable insights on where your applications stand and what needs attention.
- January 2025
PowerSchool Breach
Cybercriminals reportedly used stolen credentials to access a support portal that lacked MFA, exposing sensitive student and parent data.
- March 2025
Jaguar Land Rover Incident
A threat actor used stolen credentials to infiltrate the company’s Jira system, allegedly stealing over 700 internal documents.
- April 2025
Verizon Data Breach Investigations Report
Verizon Identifies Stolen Credentials as Top Breach Entry Point In their latest report