It's no longer "who has access."
(Well, it is, but it's not the only important question)
It's "what actually happened."
That's the shift.
Who invoked the agent? What permissions were active in that moment? What path did it take across systems?
Not what should happen. What did.
If you can't answer that, you don't have control. You have assumptions.
What we (usually) tend to ignore, or push to later
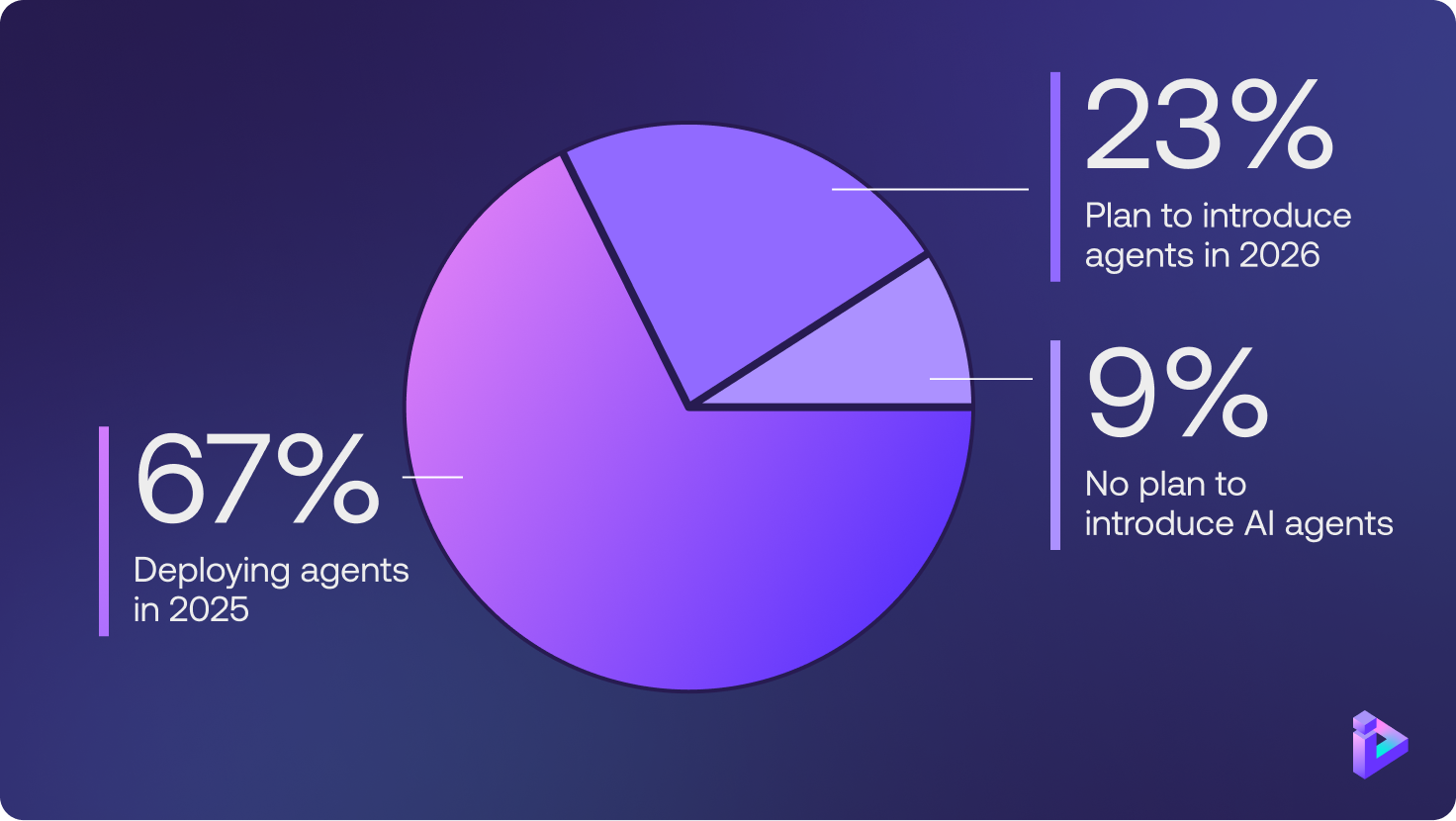
Two-thirds of enterprises already have agents in production.
Most are handling identity the same way. Treat them like service accounts. Assign a credential. Ship it. Move on. And hope for the best.
I get it. It's the path of least resistance. And it works okay - right up until you actually look at what the agent did.
Because agents don't behave like other NHIs.
They explore like a human. They move like a machine. And act on behalf of an existing identity, which means they carry everything tied to it.
The current permissions. The access decisions from two years ago. The credentials from the system migration nobody cleaned up because, honestly, it seemed fine at the time.
A single agent can move across multiple applications, reuse permissions granted before anyone imagined an agent would touch them, and reach systems that were never part of the plan
All technically allowed. None of it was what you had in mind.
Agentic identity is human identity's next evolution - and it inherits every unsolved problem from the layer below.
Agents don't create dark matter. They find it, pick it up, and move through it at machine speed. See why their “laziness by design” poses such a great risk.
Your IAM stack knows what you intended. It has no idea what actually played out.
What we built
When we started Orchid, the bet was simple: the only way to close the gap between what you intend and what actually runs is to work at the application layer. Not the IAM dashboard. Not the policy. The layer where identity actually executes.
Three years later, agents showed up and proved that bet harder than we expected.
So we extended the Identity Control Plane to cover them - the same founding principle, applied to a new class of actor that breaks every existing model.
Three new capabilities. All of them, things I wish had existed eighteen months ago.
- Agentic Observability.
See every agent in your environment alongside every human, machine, and service - at the point of execution. What they touched. What they were cleared to do. What they went ahead and did anyway. Not a policy view. A live one. - Agentic Delegation.
Link every agent to the identity it's acting on behalf of. Align permissions to the real delegation chain - not whatever was configured before agents were a thing. If the operator can't access something, neither can the agent. Human → agent → action → system. Mapped. Held. - Agentic Safe Enablement.
Wire up your existing applications to handle agents safely. Least-privilege enforced live. Full trail from action to outcome. Not the log you check the next morning. Control while it's happening.
Three questions worth answering before your next deployment
- Can you see every agent operating in your environment right now?
- Do you know what identity each one is acting on behalf of?
- Can you trace a single agent action back to the human who triggered it?
If the answer to any of those is "not really" - that's the gap.
That's where the truth is.
That's where control starts.
So, where to go from here?
If any of this resonates - and if you're running agents, it probably should- the best next step is to see it for yourself.
Actually, look inside your environment. See what's running, what's inherited, and what's executing on behalf of identities you may not have reviewed in years.
That's what Orchid does. It's what we've always done.
If you want to understand what's really happening in your environment, and what your agents can actually do - start here.
We'll show you what your IAM stack can't.




.png)