Identity Dark Matter Continues to Expand and Erode Enterprise Identity, Resulting in a Fragile Foundation for Agent AI Readiness and Adoption
NEW YORK, May 19, 2026 - Orchid Security, the company solving identity at its core, today released its Identity Gap: 2026 Snapshot, revealing that the majority of enterprise identity now exists outside the view of identity and access management systems. According to the report, invisible identity (“identity dark matter”) now outweighs visible identity across enterprise environments, 57% to 43%.
The finding comes at a critical moment, as organizations rapidly deploy AI agents. Traditional IAM was built to govern people. It was not built for autonomous systems that inherit credentials, act without human oversight, and often operate within the blind spot that identity dark matter creates.
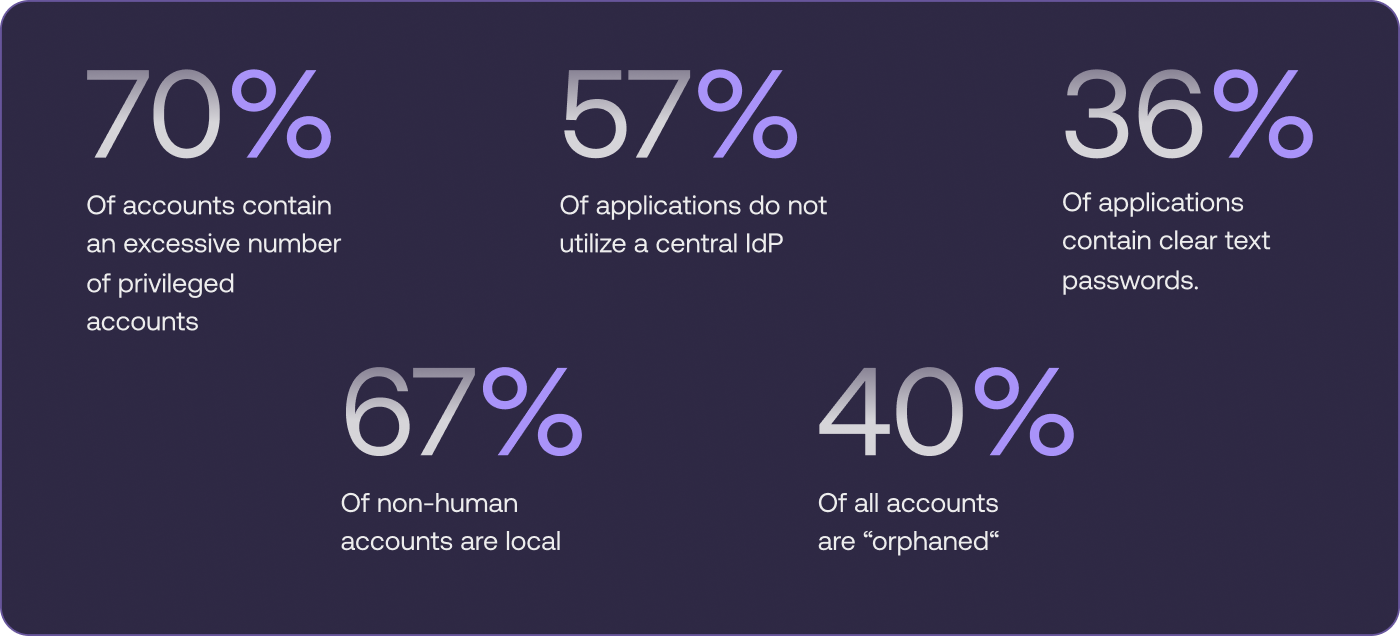
Among the report’s most significant findings,
- 67% of non-human accounts are created directly within the application, unseen and unmanaged by IAM programs.
- 70% of enterprise applications contain an excessive number of privileged accounts, dramatically increasing the potential impact of misuse or compromise.
- 57% of applications bypass centralized identity providers.
- 40% of accounts are orphaned, remaining available after their users have gone.
- 36% of all credentials are hardcoded and in clear text within applications.
“Enterprise identity has crossed a dangerous threshold: the identities we can’t see now outnumber the ones we can,” said Roy Katmor, CEO and co-founder of Orchid Security. “That was already a major security and compliance problem. In the agentic AI era, it becomes an operational crisis. AI agents don’t wait for quarterly reviews. They act in real time, across systems, using whatever access the enterprise makes available to them. If organizations cannot see every identity, understand its authority, and govern its actions, they are not ready to safely scale AI.”
Nonhuman Accounts Are a Huge Blindspot, At the Worst Time
The established IAM model for non-human identities has always carried risk: these accounts are typically granted broad, standing access locally (67% of the time, according to analysis of enterprise applications), based on the assumption that their behavior is predetermined and repetitive. A machine, service, or bot that runs the same job on the same schedule poses a risk, but one limited by its code.
However, that all changes with the latest emerging class of actor, Agent AI. While technically nonhuman, Agent AI are far from predetermined and repetitive in their actions. Rather, they are unpredictable and relentless in pursuit of their prompt. Allowing them to run unseen and unmanaged poses a huge risk.
Applications are Overpermissioned, Unmanaged, and Vulnerable
There is a growing disconnect between formal identity controls and how access actually functions. While many organizations have strengthened corporate IAM systems—with a strong stack consisting of a centralized identity directory, strong authentication from an identity provider (IdP), privileged access management (PAM), and increasing identity governance and administration (IGA)—Orchid found that these controls are frequently bypassed. Consider that almost 3 out of 4 applications have excessive privileged accounts, more than 1 out of 2 applications allow authentication through local or unmanaged pathways, and 1 out of 3 applications contain credentials stored in clear text, embedded directly in code or configuration files.
These all contribute to the expanding layer of unmanaged access, or “Identity Dark Matter,” eroding the foundation of identity at its core. “Organizations have invested heavily in securing the front door, but the research shows identity risk is increasingly concentrated in the side doors: local accounts, unmanaged access paths, hardcoded credentials, and excessive privileges that sit outside formal controls,” Katmor said.
Compounding Risk: The Rise of “Toxic Combinations”
Beyond individual exposures, the report identifies what Orchid calls “toxic combinations”—overlapping identity gaps that significantly increase risk.
Examples include:
- Orphaned accounts with elevated privileges
- Applications that bypass centralized identity providers while storing credentials in cleartext
- Dormant accounts operating without logging or oversight
Individually, these gaps are concerning; together, they create unmonitored access paths that can dramatically increase the potential level of compromise.
AI Agents Are Accelerating Identity Exposure
As organizations rapidly deploy AI agents to automate business processes, these identity gaps are not only increasing but are also becoming more visible and more exploitable.
Designed for efficiency, AI agents intuitively identify and utilize the most direct access paths available, including those outside centralized IAM controls, regardless of whether those accounts, credentials, or permissions were intended for their use.
“AI agents discover and exploit identity control gaps and exposures in a way and at a speed we’ve never seen before,” Katmor said. “If there’s a shortcut in your environment, an autonomous system will find it.”
A Growing Gap Between Identity, Intent, and Reality
The findings suggest that many organizations are approaching Agent AI implementation with an incomplete understanding of how access actually works across their environments, often without realizing it. This prevents the necessary risk management that accompanies the advent of AI Agents.
Without first shoring up the foundation of enterprise identity (each application), enterprises expose themselves to increasing cyber, compliance, and operational risks—now at machine scale.
“Identity programs look strong on paper, but most identity activity happens outside them,” said Roy Katmor, CEO and co-founder of Orchid Security. “That’s where security, compliance, and AI risks really start to build.”
About the Report
Identity Gap: 2026 Snapshot is based on anonymized telemetry collected from enterprise applications deployed across North America and Europe between April 2025 and March 2026. The data spans industries including financial services, healthcare, retail, manufacturing, and energy, and reflects both managed and unmanaged identity activity across enterprise environments.
About Orchid Security
Orchid Security sees straight into the application binary to deliver the industry’s first Identity Control Plane, transforming IAM complexity into clarity, compliance, and control. Its Identity-First Security Orchestration platform continuously discovers enterprise applications, analyzes their native authentication and authorization flows, and accelerates onboarding into governance systems, putting true identity insight in front of security leaders and practitioners, without the months of manual work traditionally required for each task or informational ask. By exposing and remediating the ‘identity dark matter’ hidden across modern environments, Orchid helps enterprises solve identity at its core; reducing risk, lowering operational costs, and achieving compliance at scale.
Media Contact:
Chloe Amante
camante@montner.com
Montner Tech PR




.png)