Identity Dark Matter Hides in Applications. Orchid Makes It Visible.
When identity behavior inside applications becomes observable and explainable, Orchid becomes the foundation of a modern identity infrastructure.


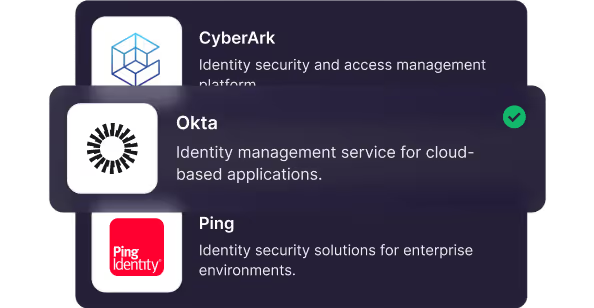
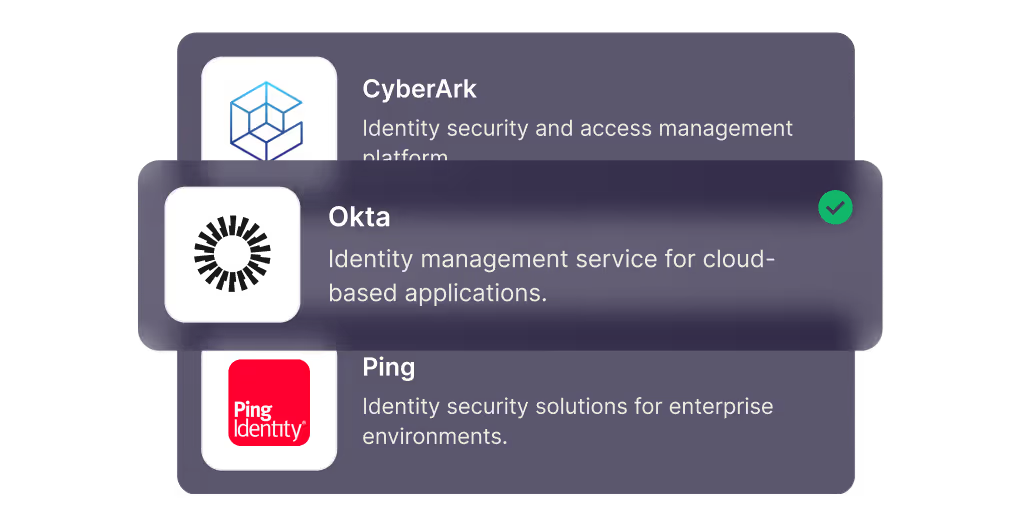
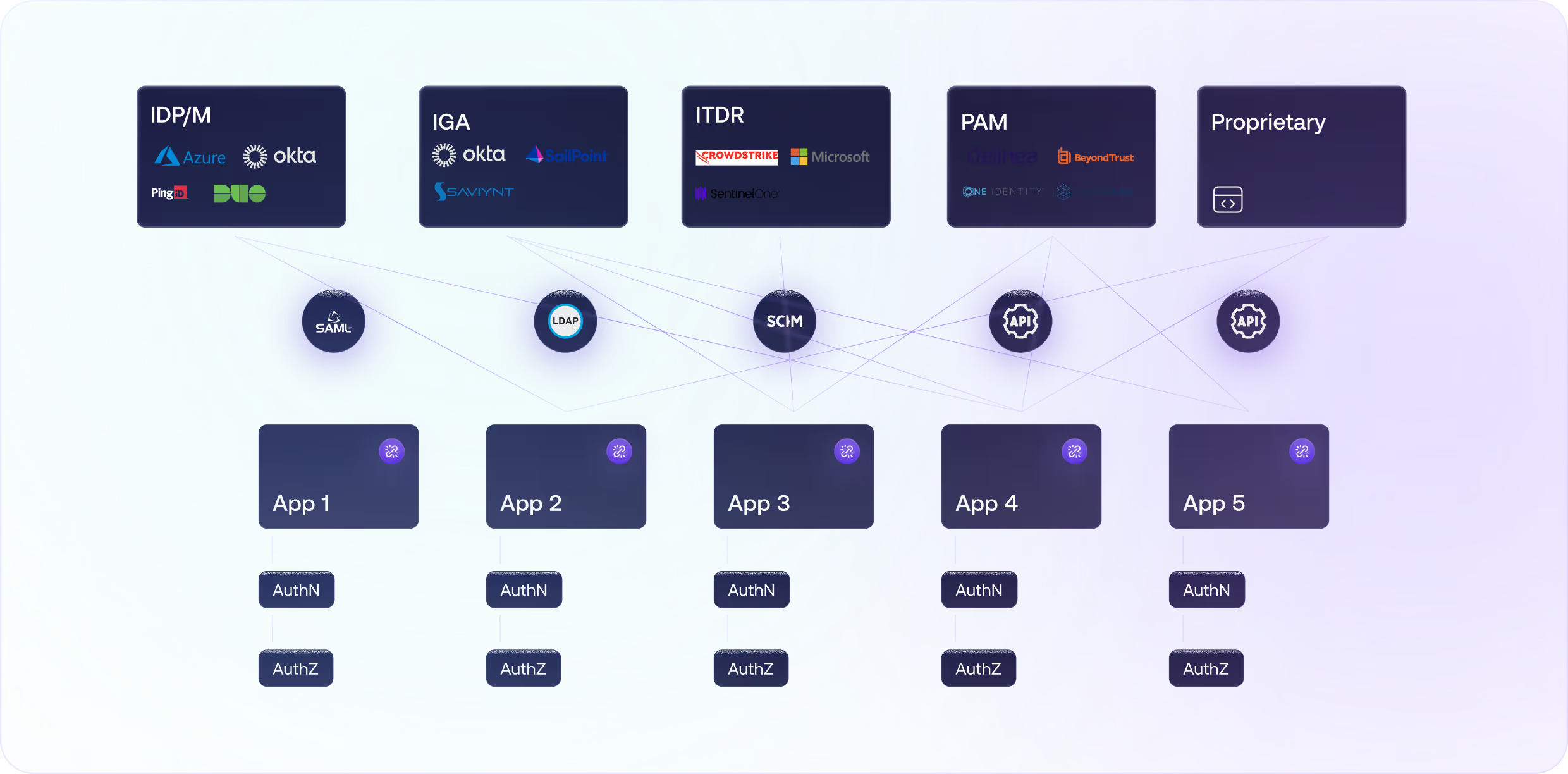
Integrating with Your IAM Stack












IAM Tools See Less and Less
IAM is a control layer. But it only sees what’s centralized. As identity logic moved into applications, critical behavior slipped out of view. That’s why Orchid exists.

The implementation of Orchid Security will have reduced the inherent friction that comes with manually onboarding applications from so many different countries and service business, improving agility and the service ISS staff provides to customers.



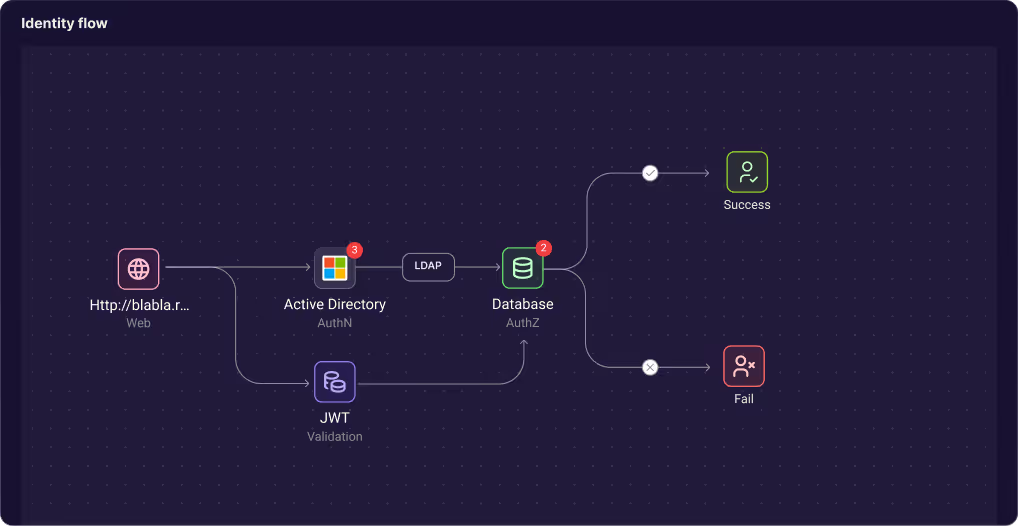
How It Works


Orchid is used by teams responsible for:
Simple, Fast, Automated


Frequently asked questions
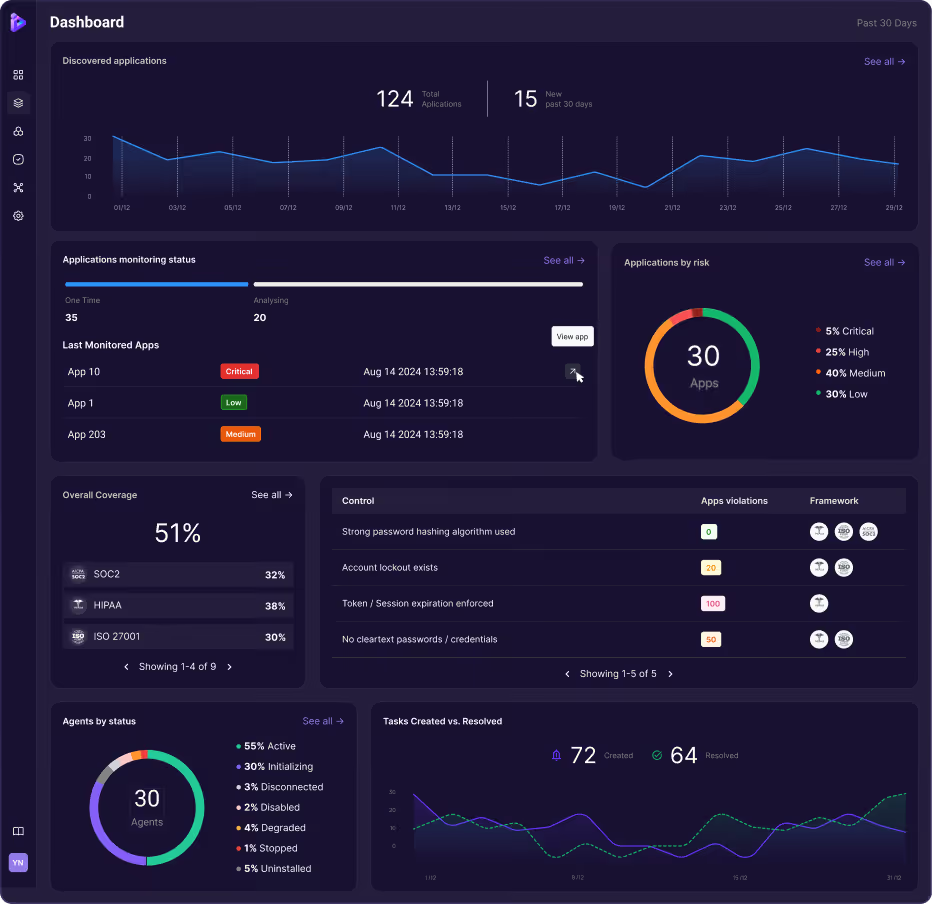
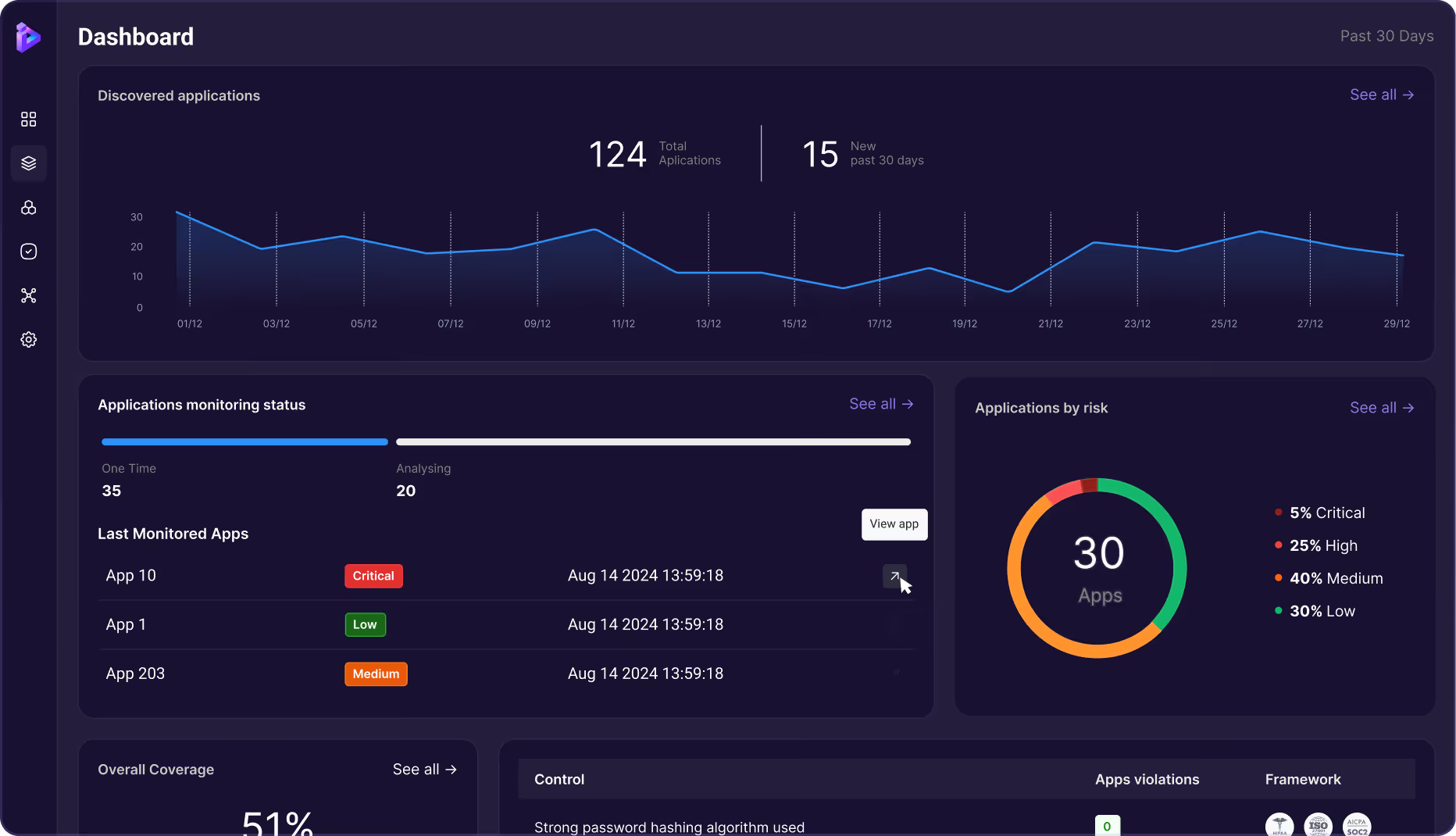
Orchid is an identity-first security platform that discovers, analyzes, governs, and proves identity controls across all applications.
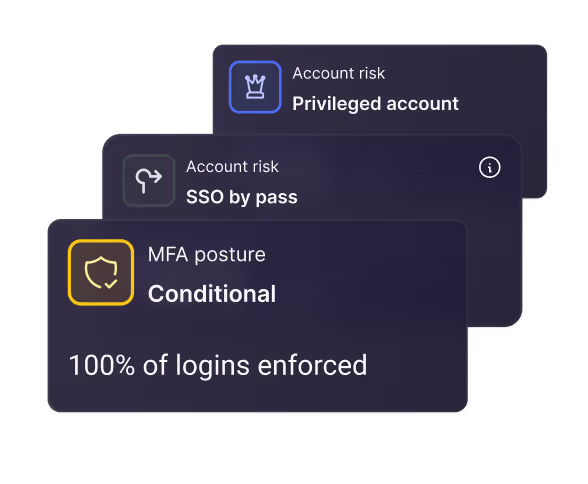
Orchid eliminates “identity blind spots” by uncovering unmanaged apps, hidden authentication flows, and ungoverned access.
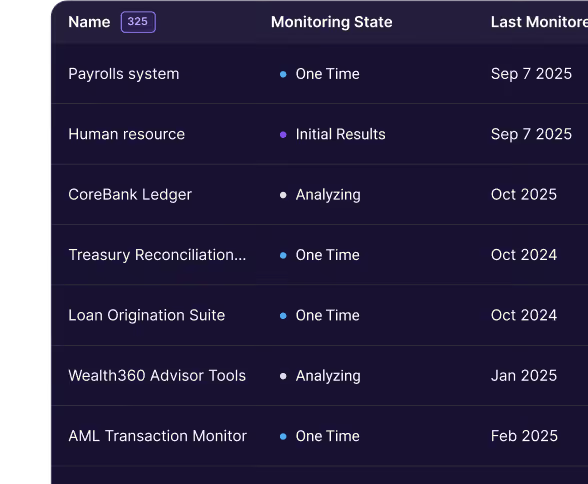
Orchid discovers SaaS, cloud, on-prem, legacy, and custom-built applications automatically.
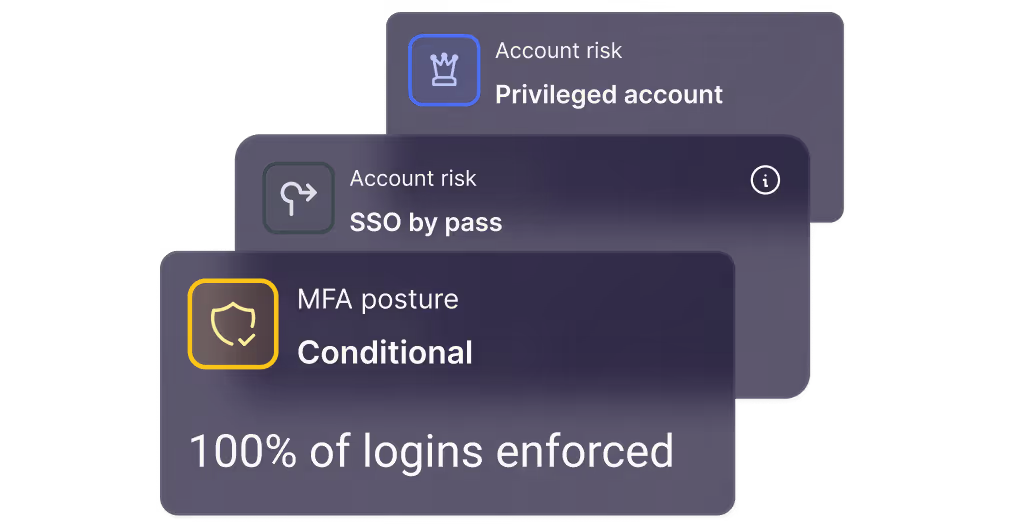
Orchid analyzes authentication and authorization flows, detects risk, enforces policies, and automates remediation.
No. Orchid integrates with existing IAM, PAM, and IGA tools to enhance visibility and governance.
Identity dark matter is access, credentials, and authentication logic that security tools can’t see or track.